Map every external connection into your environment
Most breaches don’t start with a hack. They start with access that already exists, and no one is tracking.
Inside your report:
- Full map of external identities (vendors, contractors, partners)
- Dormant or unnecessary access
- Over-permissioned accounts across SaaS tools
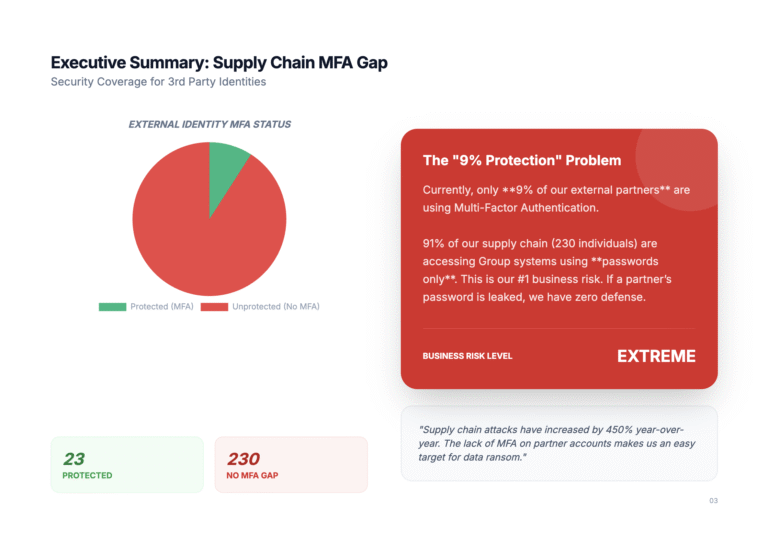
- External connections lacking basic controls (e.g. MFA)
- Early risk indicators based on unusual access patterns
Ready to secure your SaaS?
No agents. No deployments. Just instant SaaS visibility.
Overview
The only SSPM platform built in the GCC, trusted globally for real-time SaaS visibility and security. Protecting organizations where traditional security ends.